These days, it feels like cybercrime is a constant backdrop in our lives. It’s like headlines of new system compromises appear every day. And it’s only going to get worse.
In 2017, 52 percent of small UK businesses fell victim to cyber security breaches or attacks. Sixty percent of these same businesses say that the attacks are becoming more severe and sophisticated.
Because of this, cyber security should be top of mind for all small business owners. We appreciate that this can be intimidating, even if you’re quite tech literate. It can be particularly daunting, when reading about all the things you need to do to protect your business. So, today, we’re going to show you one simple step to protect your business from attack.
Over 92 percent of malware infects your business via email. This is what we call a ‘phishing’ attack, and it is the most likely to catch you and your employees out. However, if you are alert to these emails, your odds of hackers breaching your business drop dramatically.
How to foil phishing attacks in one simple step
Phishing email attacks always take a very particular form. The email contains a link the attacker wants you to click. Attackers hide the real destination of the link from you. Normally, they present it in a benign way, like as a button for you to click.
Thankfully, it’s not hard to discover the destination of any link within an email. All you need to know is one simple technique – the ‘mouse-over’.
Use ‘mouse-over’ to uncover the real destination
Hover your mouse pointer over a link to reveal its full address. It will normally appear in the bottom left-hand corner of your screen. Try it with the link below:
www.safe-website.co.uk
You should see the real link destination as www.dodgy-website.co.uk.
Although this technique works for both laptops and desktops, there is a slightly different method for touchscreen devices.
To reveal the true web address, you must press and hold the suspicious link.
Warning: Make sure you don’t just press the link and let go. Otherwise you’ll be doing exactly what the attacker wants. It is vital that you hold your thumb or finger down until the address pops up.
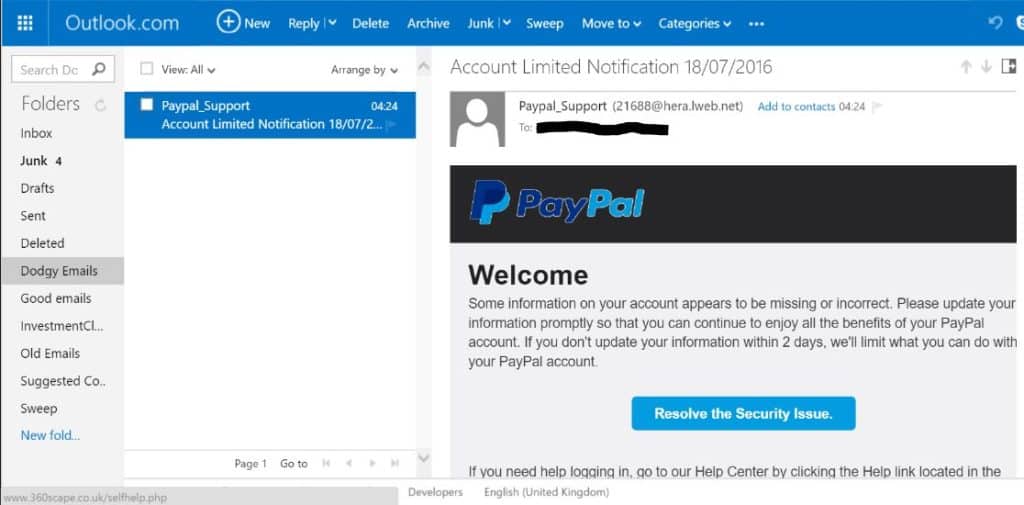
Our phishing trip with ‘PayPal’
Here’s a real-life example to help you with this technique. Below you will see a phishing email sent to me from ‘PayPal’, promising to “Resolve the Security Issue”. You will find the content of phishing emails are purposefully vague. This is to try to entice you into clicking. Don’t fall for it. Your curiosity may not kill the cat, but it could cause serious damage to your business.
When I hovered my mouse over the button the underlying link appeared in light grey at the bottom left-hand corner (you might need to zoom in to see it).
But how do I read a web address?
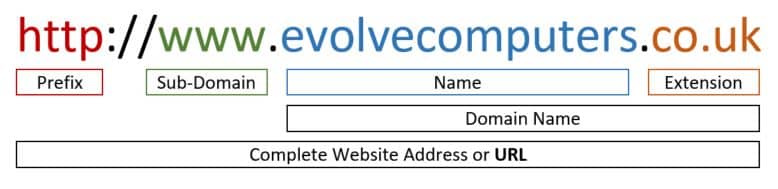
The next step to this technique is knowing how to interpret the web address you reveal. The key here is the ‘domain name’.
Below you can see the full address of our website broken down into its parts. The domain name portion is evolvecomputers.co.uk. This is a valid address and you can double check by typing it into Google and reviewing the search results.
If the domain doesn’t match who sent you the email something is wrong. Do not click on the link and delete the email for good measure.
Of course, it’s not always that simple. Attackers will try to confuse you with sub-domains. In the image below the sub-domain makes it look like the link goes to Evolve Computers. But, if you look at the domain name – dodgydomain.co.uk – you see the true destination. This is a common tactic, so be vigilant when inspecting addresses.
Recap: the ‘mouse-over’ technique
Here’s a quick reminder of what you’ve learned today:
- Being alert to ‘phishing’ will protect you from most threats
- If in doubt, mouse-over to check the web address
- On a mobile device press-and-hold the link to find the real destination
- Still not sure? Call your IT company
Download your Cyber Essentials Questionnaire
We hope that this quick tip helps you prevent phishing attacks from disrupting your business growth.
If you’re wanting to ensure that your cyber security is up to scratch, why not download your free Cyber Essentials Questionnaire and IT policies. It’s the first step to achieving Cyber Essentials accreditation, which proves you meet the minimum requirements for a secure business.
You can also purchase our companion guide to the questionnaire. Not only will it give you detailed answers to every question, but it includes two free half-hour sessions with our Cyber Essentials experts.
If you have any questions or would like to discuss cyber security further, don’t hesitate to get in touch today.